(Folders vs. Metadata by John Norris is licensed under CC BY-SA 2.0 )
By: Rajat Bhardwaj
A bill amending the Telecommunications (Interception and Access) Act of 1979 was recently introduced in the House of Representative of Australia’s Parliament. This bill marks yet another initiative by governments to ensure national security though surveillance of Internet traffic, forcing telecommunication companies to retain user data for two years. This amendment is designed to allow warrantless access by specified ‘criminal law-enforcement agencies’ – a list that the Attorney General may expand. Further, these agencies may access user data for a variety of reasons including civil investigations such as non-commercial copyright infringement. On the contrary, other organizations like the Australian Competition and Consumer Commission, the Australian Securities and Investment Commission, and movie studios would cease having warrantless access to data such as phone records.
Although these efforts to limit access to user data are commendable, they should be treated with a degree of skepticism. In Communications Minister Malcolm Turnbull’s presentation of the proposed legislation, he outlined the parameters of the amendments, including the categories of metadata retained. Mr. Turbull stated that ISPs are not required to retain substance or content of any communication, including e-mail subject lines or social media postings. The two-year data retention excludes web browsing history or personal locational data. Mr. Turnbull emphasized that the bill does not grant agencies with new powers; rather, provides the same types of information as in legitimate investigations subject to the strict limitations.
The bill reduces the number of agencies with warrantless access to data but simultaneously gives the Attorney General the power to declare additional agencies. The data retention regulation only applies to six categories of metadata:
– Subscriber/ service data; source of communication
– Destination of communication
– Date, time, and duration of communication, or of its connection to the service
– Type of communication, or type of service used in connection with a communication
– Location of equipment or a line used in connection with a communication
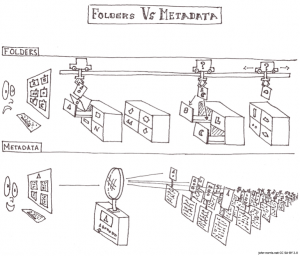
In practice, however, the retention of metadata can potentially reveal incredibly sensitive information, including files on the user’s computer. Although the bill explicitly excludes content, metadata may inevitably be compiled to disclose websites visited, cookies and cached data, and login details with auto-fill features, providing a complete profile of the user.
As for copyright infringement, iiNet, Australia’s second largest ISP has vowed to protect customer privacy and provide only information necessary to the data retention bill. iiNet previously fought a four year legal battle in 2012, where thirty four studios alleged that the ISP was responsible for infringement by its customers. The High Court of Australia held that the Copyright Act did not put a positive obligation on ISPs to interfere with customer’s online actions.
Mr. Turnbull said in a press conference that government agencies are not interested in going after those infringing copyright online but rather focused on national security concerns. The investigative means, however, that the bill provides law enforcement agencies is slightly frightening, even with its limitations.

You must be logged in to post a comment.